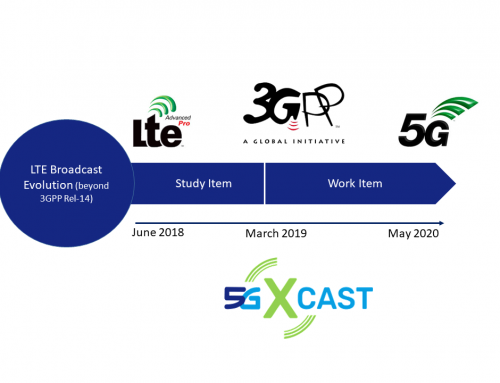
5G-Xcast is proud to announce that deliverable D5.3 on Application Layer Intelligence is now released and can be downloaded from this link.
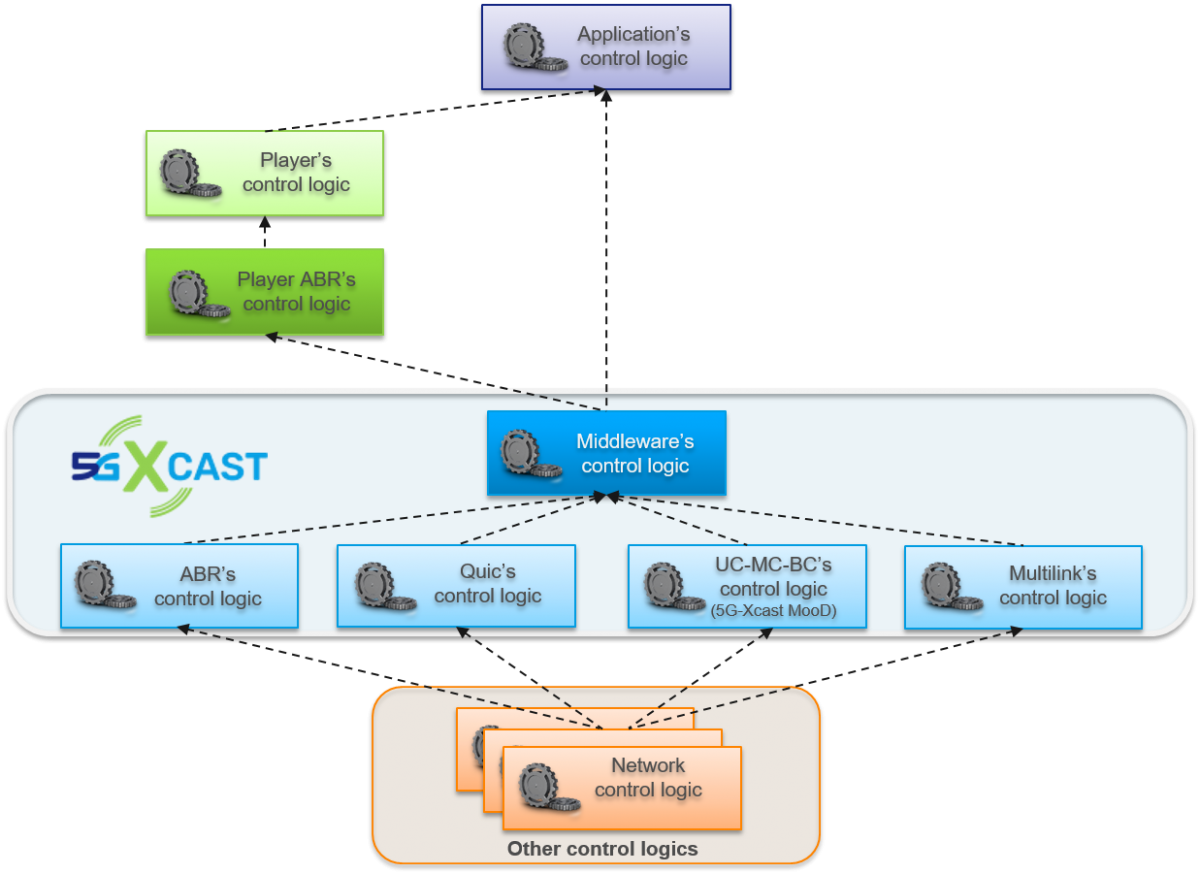
A core principle of the 5G-Xcast approach to content delivery is to insert multicast into an otherwise unicast path. We treat multicast as an internal optimisation capability which should have minimal impact on the uncast logic of the higher protocol layers, including the application layer. However, a range of optimisation techniques have been deployed over the years with the assumption that the final hop, from edge server to client application, is unicast. The insertion of multicast into this path will break the unicast assumption and therefore has the potential to disrupt these optimisation techniques. In this document we analyse the impact of the insertion of multicast into the delivery path on such optimisation techniques. Where applicable, we discuss negative impacts, but on the whole, most of the optimisation techniques are still effective and do not prevent the use of MC.